Practical attacks on web crypto
Erlend Oftedal
—
@webtonull
Bekk Consulting
7. December 2011
Erlend Oftedal
—
@webtonull
Bekk Consulting
7. December 2011

What's the best way to anger a security guy?
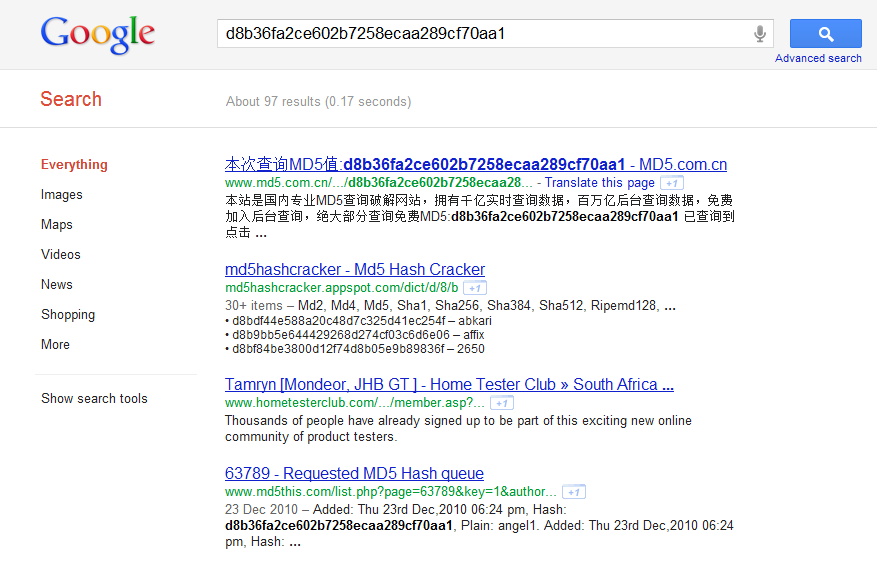
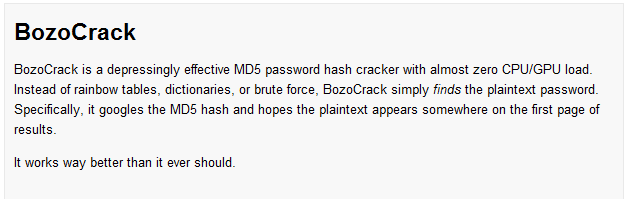
Given a password hash, what is the easiest way to find the password?
GET /
200 OK ... <a href="/resource/?a=123&b=46&signature=LQWJDQOC21ASDiojoQ2e13lkajsd="></a> ...
GET /resource/?a=123&b=46&signature=LQWJDQOC21ASDiojoQ2e13lkajsd=
200 OK Data authorized by signature...
Signature = md5(secret + data_to_sign)
H0 = MD5_round(s, D0)
Hn = MD5_round(Hn-1, Dn)
MD5(secret + data) = h(secret + data + padding)
secret + data + padding + some other data
MD5(...) = h(secret + data + padding + some other data + padding)
Hx = MD5(secret + data)
MD5(secret + data + padding + new data)
H0 = MD5_round(Hx, D'0)
bar=2&baz=3&foo=1
SECRETbar2baz3foo1
bar=2&baz=3&foo=1&signature=afb12318a0b9823bcd
bar=2&baz=3&foo=1and
b=ar2baz3foo1
b=ar2baz3foo10000020&bar=6&baz=5&foo=4and then length extend the signature to include the new parameters
GET /
200 OK ... <a href="/resource/LQWJDQOC21ASDiojoQ2e13lkajsd="></a> ...
GET /resource/LQWJDQOC21ASDiojoQ2e13lkajsd=
200 OK Secret data....
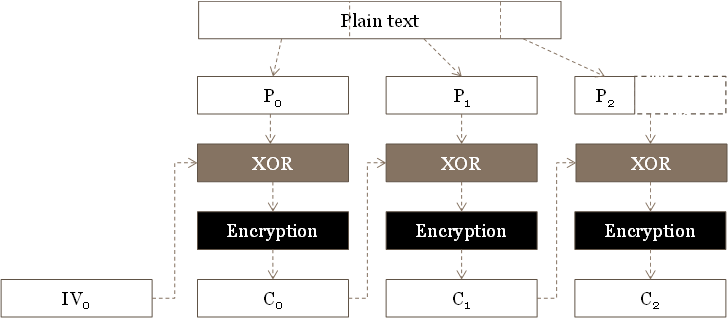
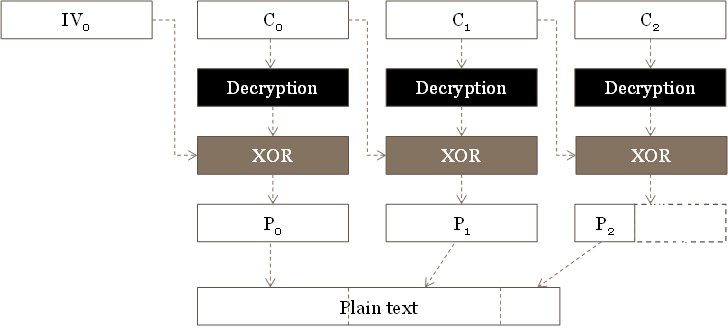
GET /resource/<IV><C0><C1><C2>
GET /resource/<R><C0>
R7 = R7 ⊕ 0x01 ⊕ 0x02
Pn = Rn ⊕ 0x08 ⊕ IVn
try {
value = decrypt(inputValue);
if (db.querySecretElement(value) != null) {
return OK;
} else {
return NOT_FOUND;
}
} catch(PaddingException ex) {
return NOT_FOUND;
}
Pm* = Pm ⊕ IVn ⊕ IVm
Pm* ⊕ IVm = Pm ⊕ IVn ⊕ IVm ⊕ IVm = Pm ⊕ IVn
[A = attacker controlled data][S = secret data]
[IV][C0=E(A + S0)][C1=E(S1-S8)][...]
Pn+i = [A + i] ⊕ IV ⊕ Cn+i-1
BONUS MATERIAL
What doesn't kill you makes you smallerSuper Mario
Questions?